We can all recall our most embarrassing moments, remembering every cringe-worthy detail that we hope others have long forgotten. But what happens when those moments get replayed on social media through posts made by our friends or acquaintances? Gone are the days of assumed privacy when every mistake, misstep, or mischief becomes fodder for online exchange.
The consequences of this type of embarrassing exposure online provide the basis for research I conducted on privacy invasion and its effects on relationships. In a paper published in Information Systems Research, my co-authors Ben C.F. Choi of the UNSW Australia Business School, Zhenhui (Jack) Jiang of the National University of Singapore, B.S. Xiao of the University of Hawai’i at Mānoa, and I examined the effects of a few key variables surrounding embarrassing social posts—namely whether or not the target was tagged in the post, and the level of commonality (i.e., shared friends) across social networks.
We assessed how these key variables influence perceived privacy invasion and relationship bonding. For the purposes of our research, perceived privacy invasion refers to the extent to which an individual believes that his or her personal information space is intruded by others, while relationship bonding refers to the extent to which an individual believes that an interaction leads to an improved social relationship.
Based on previous research related to these topics, we speculated that posting with tagging would lead to higher levels of perceived privacy invasion than posting without tagging. However, we anticipated that this outcome would be moderated by the level of network commonality. In terms of relationship bonding, we predicted that posts from an acquaintance in a low-commonality environment would be perceived as a direct humiliation, while posts from a closer friend in a high-commonality environment would be viewed more positively as good-natured teasing.
Putting tagging to the test
To test our hypotheses, we created a mock Facebook platform and asked subjects to react to hypothetical embarrassing posts—some with tagging and some without—in environments with either high or low network commonality. The results supported many of our initial assumptions.
In general, we found that posting with tagging leads to a higher level of perceived privacy invasion than does posting only. However, the number of friends in common plays a major role in determining the measure of perceived privacy invasion.
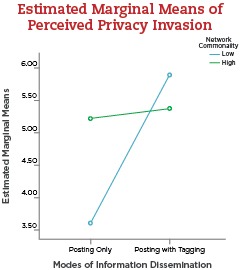
In the instance of low network commonality—meaning that the target and the disseminator have few shared friends—the target assumes that a post without tagging will have an audience limited to only the disseminator’s friends, so the perception of privacy invasion remains low. However, when that post is tagged, the audience is expanded to the target’s friends, and therefore, the level of perceived privacy invasion increases.
On the other hand, when the target and the disseminator share high network commonality, the post is widely viewed regardless of whether or not it was tagged, so the perception of privacy invasion varies less based on tagging than when network commonality is low. (See Figure 1.)
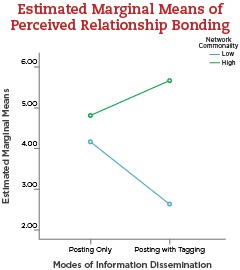
In terms of relationship bonding, our study revealed that posting with tagging is associated with significantly lower perceived relationship bonding than is posting-only when network commonality is low. This supports the notion of tagged posts being interpreted as a direct humiliation that would warrant a tendency for the target to pull away from the disseminator. Conversely, posting with tagging is associated with significantly higher perceived relationship bonding than is posting-only when there is high network commonality, as the embarrassing post can be regarded as friendly teasing, leading to enhanced rapport between the parties involved. (See Figure 2.)
One final aspect of our research looked at how a target chooses to respond to privacy invasion, by either avoiding or pursuing future interaction with the disseminator. Not surprisingly, a strong perception of privacy invasion prompted targets to withdraw from an embarrassing exposure. However, targets were reluctant to completely avoid future contact with the disseminator (e.g., by ‘unfriending’ him or her, or reporting the disseminator to Facebook), possibly due to the concern that such actions would trigger direct confrontations.
Post with caution
In sum, our findings show that both the way information is posted (either with tagging or without) and the level of network commonality influence perceived privacy invasion and relationship bonding.
My advice to users of social media is to be aware of how your posts can affect relationships, particularly with the use of tagging. Be mindful of not only the content of your posts, but the scope and size of their audience. My findings also have potential technical implications for the Facebook platform itself. In light of this research, Facebook could consider enabling new features that allow users to tactfully de-escalate their online relationships by gradually excluding disseminators from one’s social networking activities. This would lead to an eventual dissolution of the online relationship, allowing victims to avoid future embarrassment.
In an era when every action we take has the potential to be replayed online, consider the possible fallout and refrain from tagging embarrassing photos or posts about others. In doing so, you may just spare yourself some online embarrassment in the future.
Read the full paper “Embarrassing Exposures in Online Social Networks: An Integrated Perspective of Privacy Invasion and Relationship Bonding,” published in Information Systems Research.
Sung S. Kim is the Peter T. Allen Professor in the Department of Operations and Information Management at the Wisconsin School of Business.
Tags: